WordPress is a widely used platform and that makes it a highly targeted platform for hackers and identity thieves. It’s important to keep your WordPress website updated with the latest security patches. It’s also just as important that you keep any modules and plugins updated to the latest versions. Hackers thrive on lazy webmasters and most hacked websites could have been kept secure simply by keeping the website up to date.
Aside from staying up to date. How can you know if your site is vulnerable to hackers and exploits? There’s plenty of tools and plugins on the web. One of my favorites and one that is pretty user friendly is a program called WPScan.
WPScan is a vulnerability assessment tool. Its purpose is to identify common security loopholes within your WordPress website and its underlying architecture, plugins. WPSCAN is open source, free to use and anyone with a little technical ability can get it up and running. Here’s how.
To run WPScan you need a Linux OS. To install Linux inside of a virtual machine on Windows you need a VMM. A virtual machine manager. For sake of simplicity. I recommend Virtual Box. Grab the version that pertains to you. Then you want to grab your favorite distro. Again. For the sake of simplicity, I would recommend Linux Mint or Kali Linux (Infosec Linux, comes with WPScan pre-installed) tho you can set WPSCAN up on almost any Linux distro.
Setting up Virtual Box for the first time can be pretty confusing if you aren’t familiar with virtual machines. I’d point you to a guide over at itfoss that explains the process in a little more detail. Don’t worry tho. It’s actually straightforward and simple once you get a grasp of the UI. If you have a AMD based x64 system. Don’t forget to turn on virtualization in your motherboard bios!
Now that you have VirtualBox and your Linux OS up and running. Lets install and use WPScan to check your WordPress website for any security issues.
To take care of any dependencies issues. You can install WPscan thru docker. So lets get started. To install docker lets grab it via curl.
$ sudo curl -fsSL https://get.docker.com | sh
That should install docker. If everything went as planned you can then start docker, tell docker to start at boot and make sure its running with..
# sudo systemctl start docker
# sudo systemctl enable docker
# sudo systemctl status docker
Now. We can pull the latest wpscan from the repo https://github.com/wpscanteam/wpscan using docker!
$ docker pull wpscanteam/wpscan
That should download the latest image of wpscan and put it in your docker. To list your docket images you can type
$ docker images
Seeming how we just installed docker and only installed the one image. You should see only the wpscan image in your list. The WPScan repository image is wpscanteam/wpscan.
SCAN YOUR WORDPRESS WEBSITE WITH WPScan
Now. To run your WPScan image from docker all you need to do is
$ docker run wpscanteam/wpscan --url www.yourwebsite.com
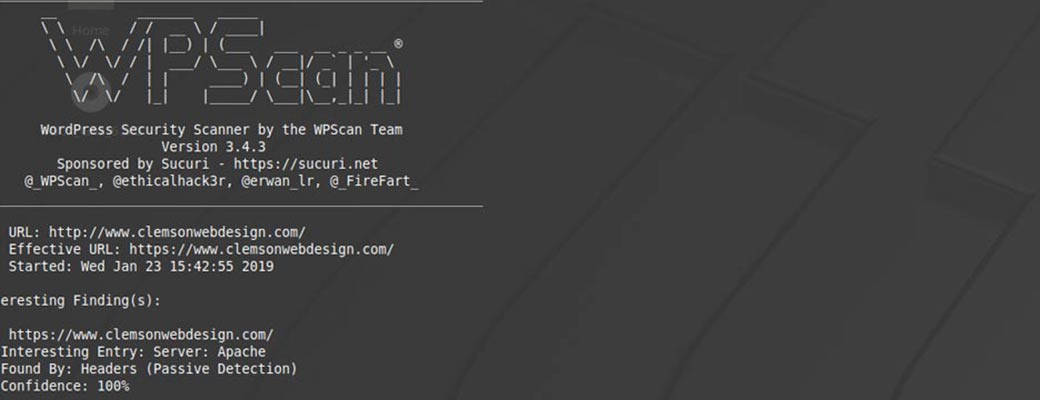
It may take a second to initialize and scan but after a few minutes you should see the results screen like below.

Thats it. WPScan is up and running. You can scan your website and identiy the lastest vulnerabilities. You can even test brute forcing against your website. To run a brute force against your site.
$ docker run wpscanteam/wpscan --url www.yourwebsite.com --wordlist wordlist_file.txt --threads 30
This tells dockers to use your wordlist_file.txt using 30 threads against your login page. To tell docker to brute force using admin as the user name only. You can do something like
$ docker run wpscanteam/wpscan --url www.yourwebsite.com --wordlist wordlist_file.txt --username admin
Last but not least. To update WPScans database of exploits. You can do the following command.
$ docker run wpscanteam/wpscan --update
If you find issues when you scan your site with WPScan. Install the latest updates on your WordPress site and then scan again.
KEEP YOUR WORDPRESS WEBSITE SECURE
If you think your website has been hacked, compromised or just you need someone to initiate a backup plan and install the latest updates. Use the contact link below.